Microsoft Sentinel SIEM Engineer
Results for ""
Maximizing the Value of Azure Automation for SOCs
A BlueVoyant Custom Levenshtein Detection What Does This Detection Mitigate? This use case has been designed to capture email spoofing attempts from an external attacker where the attacker impersonates an internal user or trusted supplier. As domain verification is not built into the Simple Mail Transfer Protocol (SMTP), attackers can counterfeit email addresses with the […]
Microsoft Sentinel Design – Updated One-Page Diagram
Microsoft Sentinel has introduced a significant number of new features and improvement of existing ones since our last diagram update. Some notable ones are increased incident management options, addition of large number of solutions including data connectors, detection rules and workbooks, content management options such as Workspace Manager, centralized data collection rules via the Azure […]
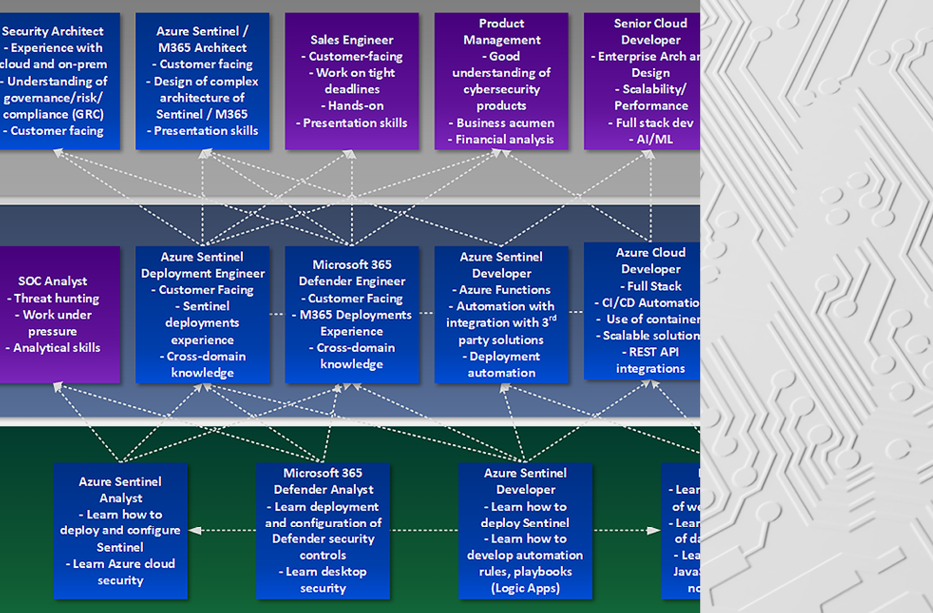
Join Our Team: BlueVoyant – Microsoft Security Consulting Potential Career Paths
In the context of a highly pace of change in technology and paradigm shifts on an almost daily basis, BlueVoyant is always looking for talented people who are flexible, willing to tackle new technologies, explore, get their hands on the latest cybersecurity tools, and literally grow with us. It is not an easy task, but […]
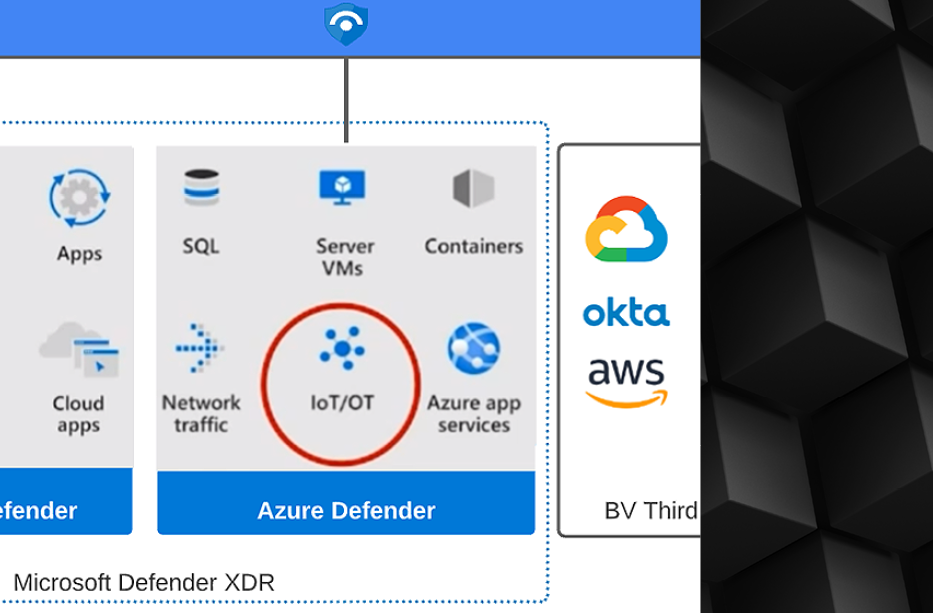
Defender for IoT Raw Log Integration into Sentinel
Microsoft Defender for IoT sensors have limited out-of-the-box capabilities to integrate their data into Azure Sentinel. Today the sensor platform supports only sending alerts to Sentinel, which is limiting since a modern SOC must have the ability to correlate any relevant sensor data that occurred around the alerts with other sources to form a complete […]
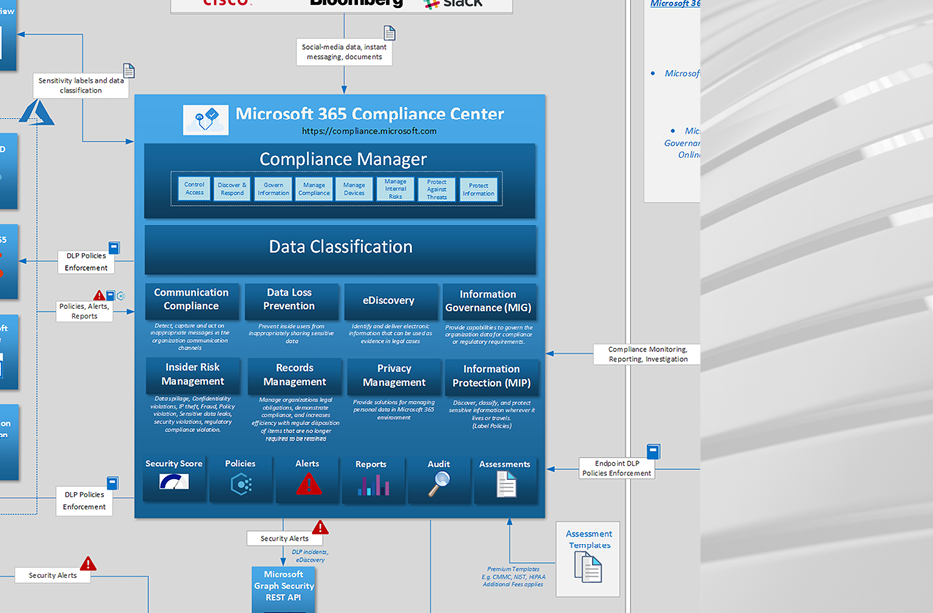
Microsoft 365 Compliance Center Design Diagram
With M365 Compliance Center, Microsoft is tackling the GRC aspect of information security. GRC has been traditionally hard to measure objectively, with CISOs having to develop their own methodologies, KPIs and governance processes. Existing standards such as NIST Cybersecurity Framework, ISO 27001, etc. help as guidelines for aligning with industry standards and avoid the need […]
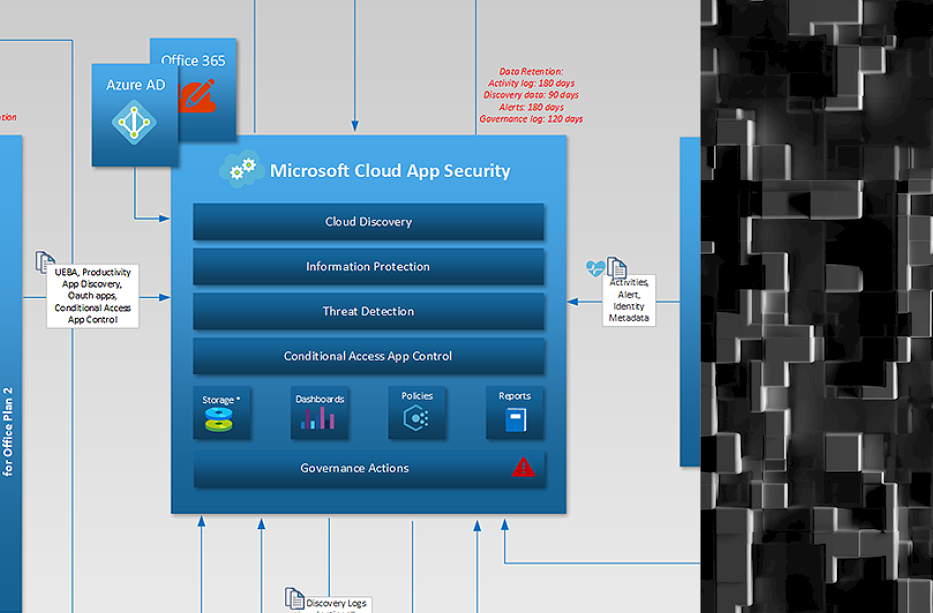
Microsoft 365 Defender, Azure Defender, Azure Sentinel One-Page Diagram
In the past we have published individual diagrams for a number of Microsoft cloud security solutions, but in the end we always intended to have the larger picture that can provide analysts with a visual understanding on what type of data is exchanged between various Microsoft security controls and how that data is used to […]
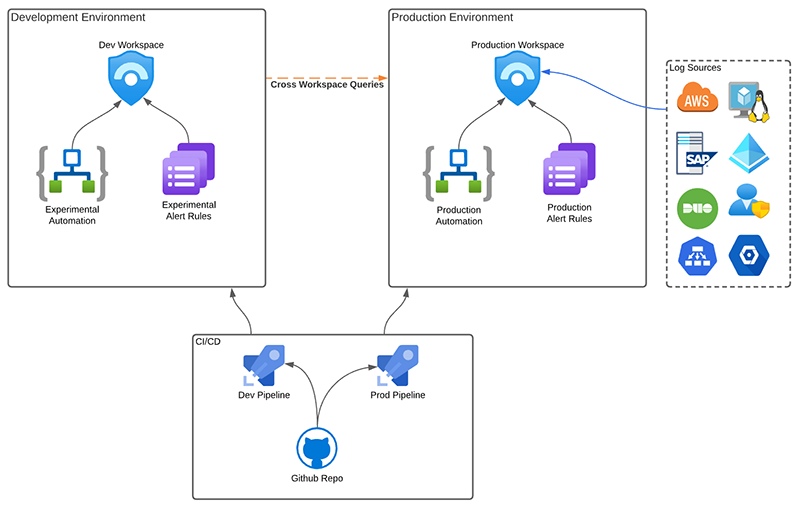
Testing With Production Data
The ability to maintain a test SIEM has been a challenge for most SOCs. Test environments are typically inadequate as SOC teams cannot rely on a limited dataset to develop and test new rules and automation. At the same time, organizations maintaining a sizeable up-to-date dataset for a development SIEM instance usually means duplicating logs, […]
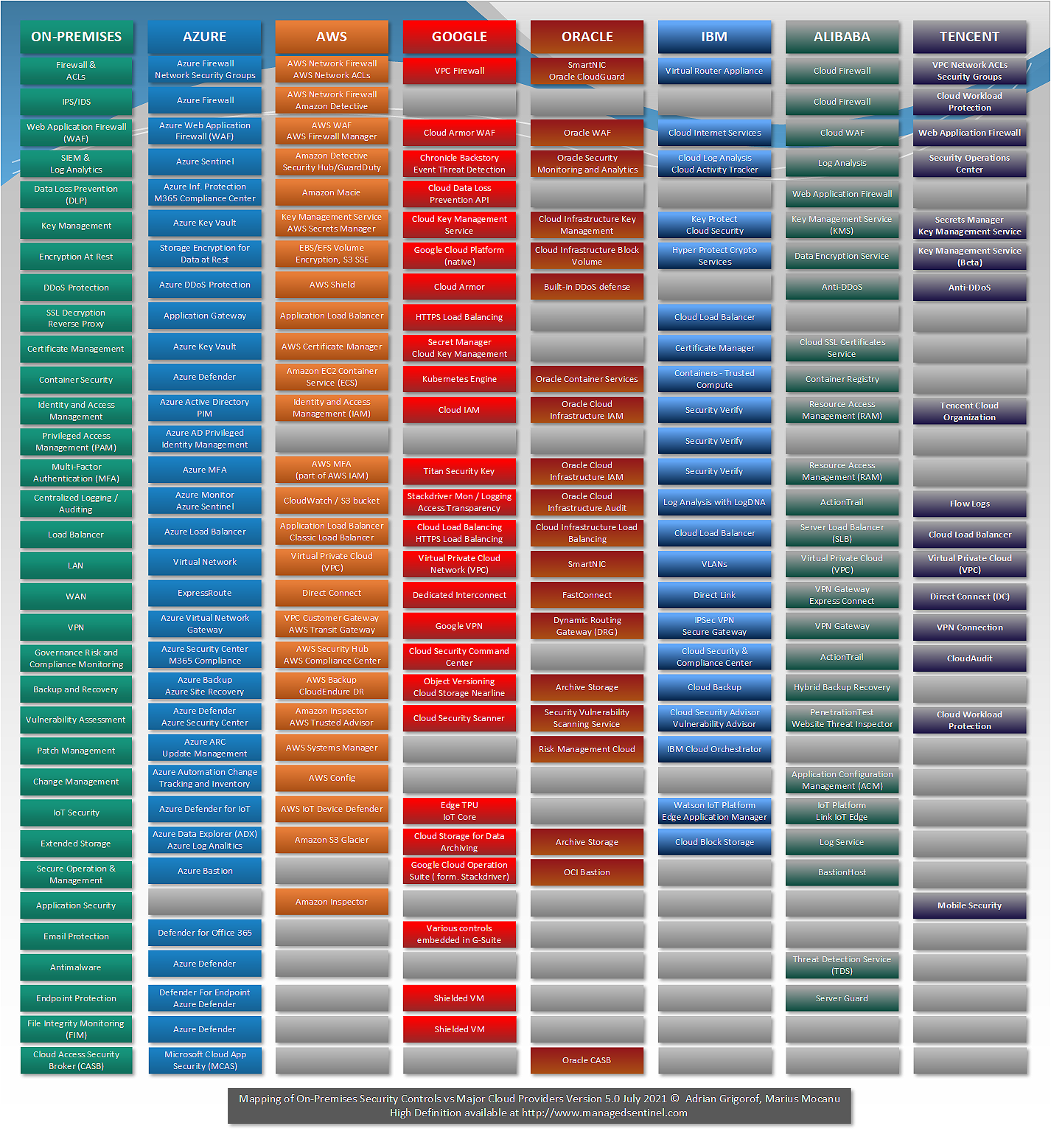
Mapping of On-Premises Security Controls Versus Services Offered by Major Cloud Providers
We are happy to publish the fifth version of a diagram that started in March 2017, with just AWS and Azure versus On-Premises. The diagram began as an effort to make a translation between the typical on-premises security controls that everybody, more or less, knows what they do and the various services advertised by major […]
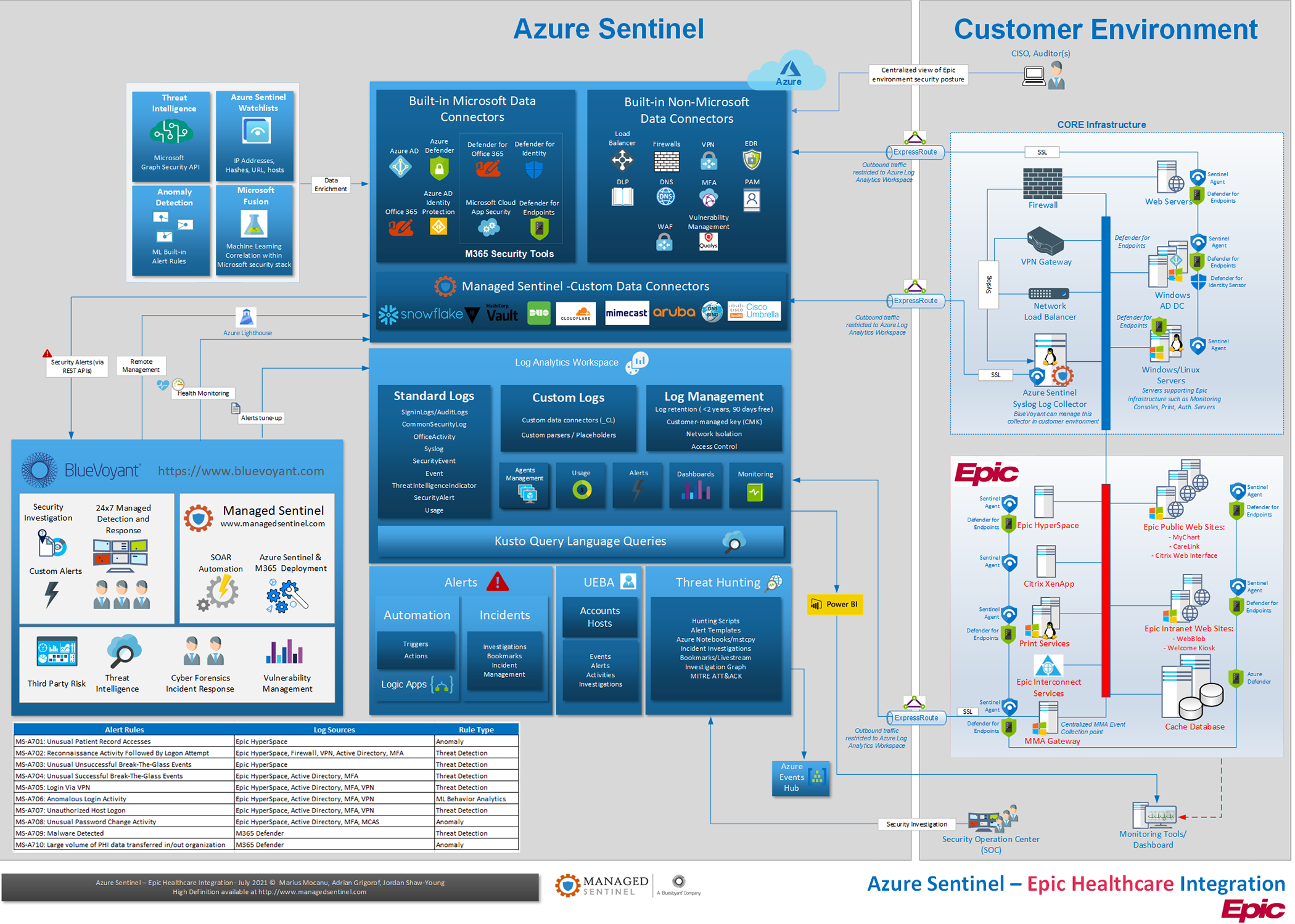
Threat Detection and Response in EPIC Electronic Medical Record (EMR) Environments
In this blog, we look at using Azure Sentinel and Microsoft XDR technologies to provide effective threat detection and response for EPIC Electronic Medical Record (EMR) environments. CISOs responsible for securing EMR systems have traditionally had a challenging task applying operational monitoring and security controls to these systems for a variety of reasons. Contractual requirements […]