Formerly known as Defender ATP, Microsoft Defender for Endpoints is now a critical component of Microsoft XDR line of security controls. Defender for Endpoints is starting to go past its newly found fame as the “new kid on the block”, with a meteoric rise in Gartner’s Magic Quadrant for endpoint protection. It is now becoming a standard against which other EDR products are matched to assess their efficiency, coverage of threats, investigation capabilities, ease of use and integration with other security controls.
We have seen Defender for Endpoints starting to make a difference the moment we deployed it for our customers, with no threat managing to go past it so far, even when distracted admins ran malicious payloads.
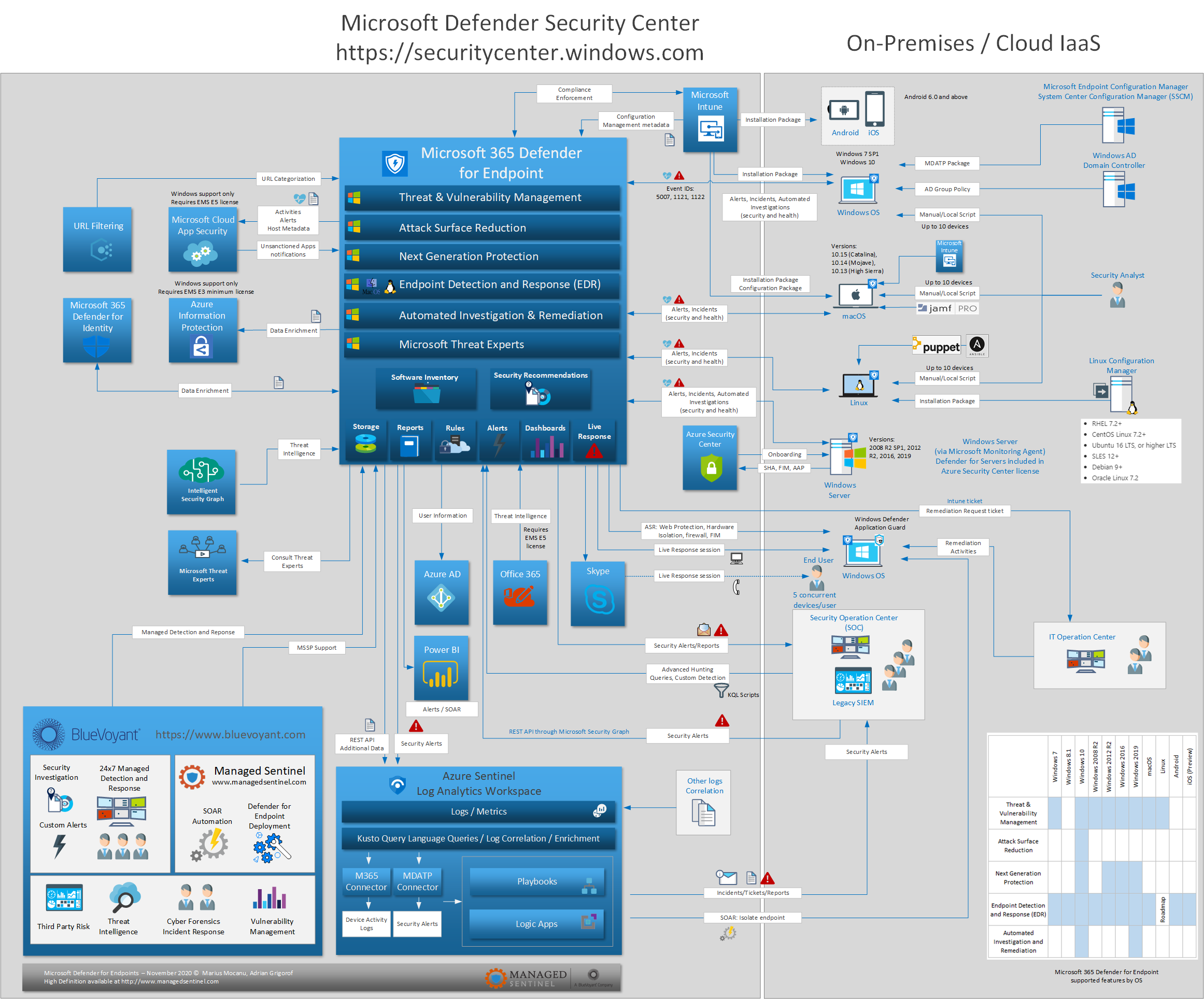
The diagram below is the next iteration of version that we published in May 2020. As usually, it is a one-page view of the core components and how other security controls interact with it. As one can see, behind the scenes, Defender for Endpoints works with a wide range of applications, gathering and sharing intelligence, and integrating with the tools that the typical analyst needs to perform their job. Other security controls, such as Azure Sentinel can either interact with through the native data connector or even go deeper through the use of rich REST API to perform tasks that traditionally required hands-on from on-premises security analysts.
Contact us for full walk-through of this diagram and a review of its integration with the overall Microsoft security stack.
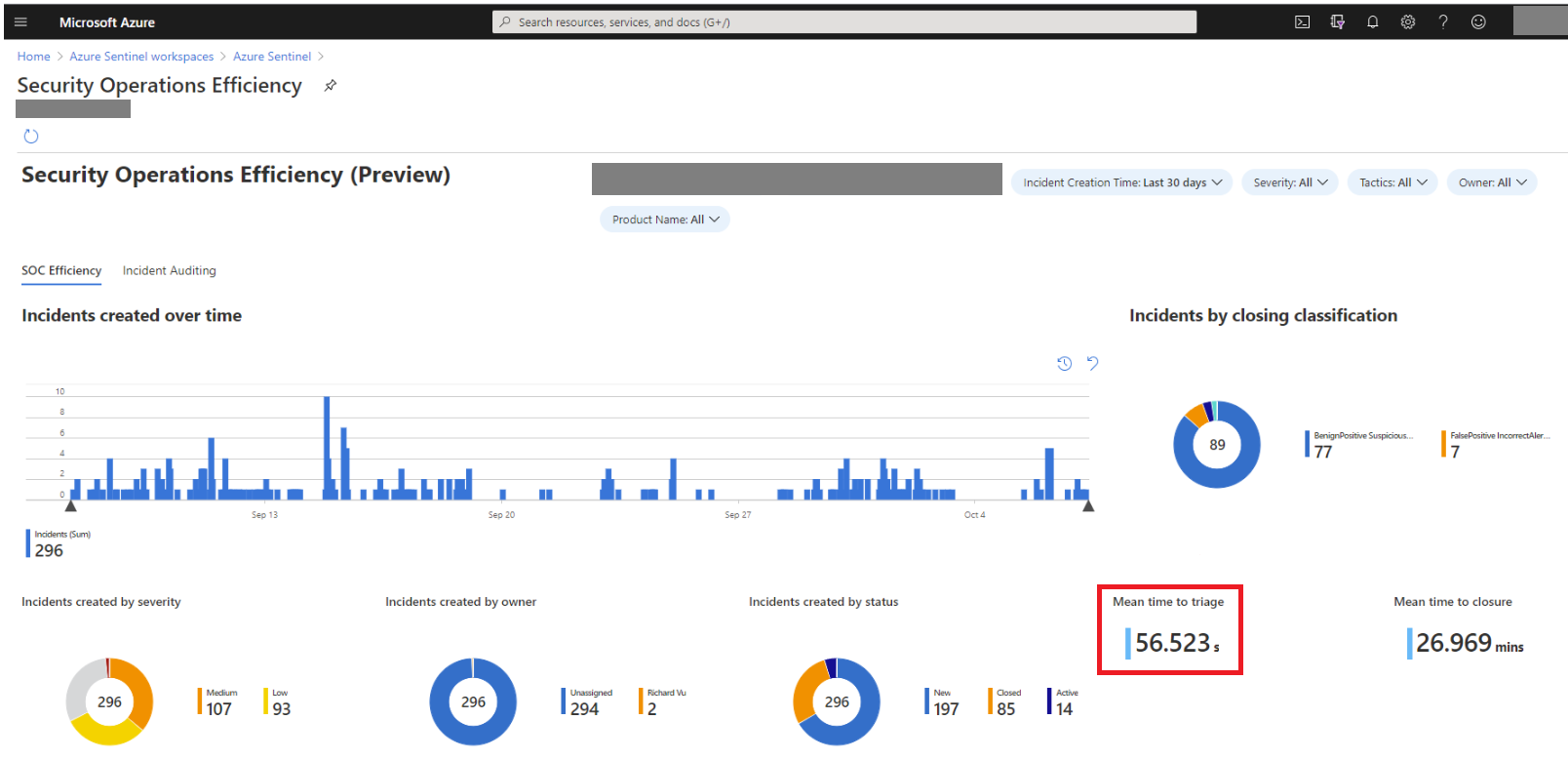
At BlueVoyant, we can assist our customers with a full deployment of Defender for Endpoints, configured to follow the industry standards and our own extensive experience based on past deployments. Our 24×7 Managed Detection and Response (MDR) service can take you to the next level, with highly trained security analysts monitoring 24 x 7 raised by Defender for Endpoints and ensuring timely remediation of the raised incidents. Our deep integration with Defender for Endpoints allow triaging of incidents within seconds and closure within minutes.